
Published by
Vishnu Siddarth
on

Introduction
Cloud costs continue to spiral for organizations lacking structured governance. Without clear policies, enforcement mechanisms, and accountability frameworks, even well-intentioned FinOps initiatives fail to deliver sustainable results. A FinOps governance framework establishes the rules, processes, and cultural foundation that transforms cloud financial management from reactive firefighting into proactive value optimization. As organizations expand beyond traditional cloud into Cloud+ environments encompassing SaaS, AI, and hybrid infrastructure, governance has become the critical multiplier that scales FinOps practices across the entire technology spend landscape.
What Makes FinOps Governance Critical for Sustainable Cost Management
The FinOps governance framework is a set of policies, controls, and mechanisms that ensure cloud and technology usage aligns with business objectives while optimizing resources efficiently. Policy defines a clear statement of intent describing how cloud-related activities should be executed to deliver business value. Governance comprises the processes, tooling, and guardrails that enforce those policies and promote desired behaviors.
Organizations cannot sustainably deliver business value from cloud without governance. Analysis of FinOps practices shows that organizations with governance policies implemented across all personas operate at Run maturity, while those without structured governance remain stuck at Crawl or Walk stages with manual processes and limited scalability.
Governance transforms FinOps from a cost visibility exercise into an embedded operational model. It's the primary mechanism for harnessing cloud power and establishing a FinOps culture—a set of attitudes and behaviors oriented toward driving business value from technology.
Key governance benefits include:
Alignment of cloud activities with overall business goals and strategies
Control over deployment and usage of cloud resources to maximize ROI
Predictable and manageable cloud costs through consistent best practices
Defense-in-depth against known threats and risks
Sustainable implementation of FinOps at scale
How Last Year's Framework Update Expanded Governance Beyond Cloud
The FinOps Framework update released in 2025 marked the evolution from cloud-only focus to Cloud+ governance. The framework now recognizes that organizations manage complex technology landscapes beyond traditional public cloud, requiring governance that spans multiple technology scopes.
"Cloud Policy & Governance" became "Policy & Governance" to reflect this expansion. Organizations now apply governance frameworks across public cloud, SaaS subscriptions, data centers, private clouds, and generative AI technologies. The framework defines scopes as segments of technology-related spending to which FinOps practitioners apply concepts.
This expansion means governance frameworks must adapt policies across different technology cost domains while maintaining consistent financial accountability. A SaaS license optimization policy looks different from an EC2 rightsizing policy, but both require the same fundamental governance mechanisms—clear rules, enforcement controls, and compliance measurement.
The Cloud+ approach acknowledges the reality organizations face in early 2026. IDC FutureScape 2026 warns that by next year, G1000 organizations will face up to 30% rises in underestimated AI infrastructure costs. Traditional cost management models prove insufficient for workloads that self-scale and can balloon budgets overnight. Organizations are experiencing what IDC calls the AI infrastructure reckoning right now.
Scope | Governance Focus | Example Policies |
Public Cloud | Resource optimization, commitment coverage | 80% compute costs covered by savings plans |
SaaS | License utilization, subscription management | Unused licenses removed within 30 days |
Data Center | Capacity planning, depreciation tracking | Server refresh cycles every 5 years |
Private Cloud | Chargeback accuracy, resource allocation | Monthly showback reports to all teams |
Generative AI | Token consumption, model costs | AI spending requires business case approval |
The State of FinOps 2025 survey, released last June, revealed that FinOps governance and policy at scale is set to become the top priority in 2026. This tracks with current reality—63% of organizations now manage AI spend, up dramatically from 31% just two years ago.
Core Components: Policies, Mechanisms, and KPIs
A complete FinOps governance framework consists of three interconnected components that work together to drive desired behaviors and outcomes.
Policies are statements of intent describing the execution of specific activities according to standards designed to deliver business value. Good policies are clear, actionable, and directly tied to measurable outcomes. For example, "80% of production compute costs must be covered by commitment-based discounts within 12 months" provides a specific target with a timeframe.
Bad policies are overly broad, lack authority, or impose disproportionate costs. "Teams should optimize costs when possible" fails because it's vague and unenforceable. The best policies balance aspirational targets with practical implementation pathways.
Governance mechanisms enforce policies through three escalating layers:
Guidelines provide advisory best practices for policy implementation. These are recommendations rather than mandates.
Guardrails establish mandatory pathways for policy-compliant actions with potential consequences for non-compliance, such as preventing deployment of untagged resources.
Automation processes automatically enforce policies, removing manual burden and ensuring consistent compliance.
KPIs measure compliance and track progress toward objectives. Governance includes both enforcement mechanisms and metrics to measure adherence. KPIs aligned with FinOps objectives are shared transparently across all personas to drive valuable behaviors.
Focus on a few strong indicators rather than overwhelming dashboards that create noise and inaction. Examples include percentage of compute costs covered by commitments (target 80%), percentage of teams trained on FinOps policies, tagging coverage rates, and budget adherence percentages. Compliance KPIs evolve over time to adapt to changing FinOps objectives.
Crawl-Walk-Run: Navigating the Governance Maturity Journey
Organizations progress through distinct maturity stages as governance capabilities evolve. The FinOps maturity model uses a "Crawl, Walk, Run" approach that enables organizations to start small and grow in scale, scope, and complexity as business value warrants.
At Crawl maturity, policies are manually created, ad-hoc, and largely reactive. Organizations aim to control significant risks to business value through basic usage and rate optimization. Policy creation is sufficient but static, with manually distributed content and training. Few metrics exist, and measurements only provide insights into benefits of maturing the function.
Teams manually check for anomalous spending and may only require rudimentary alerts. Resource tagging and cost allocation are inconsistent. The primary goal is visibility—pulling data together, cleaning it, and making sense before the next "where did that cost come from?" call lands.
At Walk maturity, standardized measures distribute best practices across the business. Cross-functional collaboration emerges as policy and governance measures are broadened. Organizations use tools that alert them and help diagnose anomalies. Resource tagging and cost allocation are standardized across most workloads. Teams have budget visibility and accountability for their spending portion.
KPIs become more specific to measure success. Optimization strategies like rightsizing or discount purchasing are applied regularly. Cost anomalies are detected and investigated quickly with alerts and governance tools.
At Run maturity, all business levels operate aligned with organizational strategy and goals. Ongoing automated policy compliance reviews provide trending data. Integration with new architectural concepts ensures currency. Enriched normalized insights and automation solutions characterize this stage.
Organizations establish various alerting thresholds to different stakeholders and automated mechanisms to resolve alerts. Governance policies exist across all FinOps personas, ranging from provisioning and allocation requirements to IAM role and ownership policies. Governance multiplies FinOps efforts by building them natively into day-to-day operations.
The goal is not to achieve Run maturity across all capabilities. Organizations should perform each capability at the minimum level that enables them to get value from operations. If Walk-stage anomaly detection proves adequate, spending time maturing to Run provides no additional benefit.
Enforcement Mechanisms: From Guidelines to Automated Controls
The three-tiered enforcement approach creates layered governance that balances autonomy with control. Each layer serves different organizational needs and represents progression toward scaled governance.
Guidelines set out best practices for policy implementation and how it can be achieved. These advisory recommendations help teams understand desired approaches without mandating specific actions. For example, guidelines might suggest tagging resources with cost center, environment, and application owner without preventing deployment of untagged resources.
Guardrails define formal processes and structures that establish mandatory pathways for policy-compliant action with consequences for non-compliance. Guardrails prevent costly mistakes while still granting developers autonomy. Every engineer makes mistakes, but guardrails ensure those mistakes don't lead to $10,000-per-day cloud bills due to an overlooked database instance.
Common guardrail examples include blocking deployment of expensive resource SKUs without approval, requiring tagging before resources can be created, and preventing non-production environments from running outside business hours.
Automation processes automatically enforce policies, removing manual burden entirely. Automated enforcement represents governance maturity and scalability. Examples include auto-tagging resources based on deployment context, automatically shutting down development environments overnight, and applying commitment-based discounts when usage patterns qualify.
By codifying FinOps governance policies, teams put guardrails in place while maintaining developer innovation. Policy enforcement must remain dynamic and flexible, allowing organizations to adjust tagging, cost constraints, and security requirements as they evolve.
Measuring Success: KPIs That Drive Accountability
Governance without measurement creates noise without action. Organizations need visibility that identifies areas requiring corrective action while driving desired behaviors transparently across all personas.
Track a focused set of strong indicators rather than overwhelming dashboards. Start with 5-7 critical tags or basic budget alerts, gather feedback, and expand gradually. Key performance indicators should align directly with business objectives.
Critical governance KPIs include:
Percentage of compute costs covered by commitments or savings plans (target 80%)
Percentage of teams trained on FinOps policies and practices
Resource tagging coverage rate (target 95%+)
Budget adherence percentage by team or project
Mean time to detect and resolve compliance issues
Anomaly response time (days at Crawl, hours at Walk, under 1 hour at Run)
Avoid tracking too many indicators, which creates inaction. A few strong indicators that drive action prove more valuable than comprehensive dashboards that no one acts upon. KPIs must evolve over time to adapt to changing FinOps objectives.
Map KPIs to FinOps processes—tagging governance, cost allocation, anomaly management, forecasting, commitment planning, optimization, and chargeback. Look for where processes lag in maturity profiles. Tighten tag compliance before tackling automated commitment purchasing. Cut anomaly response time before attempting predictive spend modeling.
Policy-as-Code: Shifting Governance Left in Development Workflows
Manual governance cannot scale with modern cloud complexity. Policy-as-code and governance-as-code embed financial accountability into infrastructure provisioning, preventing expensive mistakes before resources reach production.
The shift-left approach embeds cost awareness, forecasting, and governance earlier in the software delivery process. Instead of waiting for monthly cloud bills to assess expenses, shift-left FinOps integrates cost estimation, tagging enforcement, and budget constraints directly into infrastructure provisioning.
Policy-as-code brings consistency, scalability, version control, collaboration, and auditability to governance. Policies are applied uniformly across all resources and environments. Automated enforcement scales to large infrastructures. Policy changes can be tracked, reviewed, and rolled back. Teams collaborate on policy development using familiar software development tools.
By integrating directly with pipeline components like GitHub and Terraform, governance features allow developers to receive cost estimates before deployment, enforce tagging requirements as code is committed, and validate budget constraints before infrastructure is provisioned.
Organizations implement this through CI/CD integration. Policies are stored in Git repositories, tested through automated pipelines, and deployed across environments. Pull requests and code reviews ensure changes happen in a controlled, traceable way.
Cloud governance-as-code automatically and dynamically applies policies in fast-changing cloud environments. Cost policies are continuously evaluated against current state, utilization, and configuration. If violations occur, automated notifications and workflows are triggered. For example, a policy could identify RDS instances older than 30 days with no connections in 14 days, notify owners, and automatically stop instances if no action is taken within seven days.
Overcoming Common Governance Implementation Challenges
Organizations face predictable obstacles when implementing governance. Resistance to policy adoption, siloed teams limiting collaboration, inadequate visibility into costs, and balancing autonomy with control represent the most common challenges.
Cultural resistance emerges when teams resist shifting to more automated, code-driven approaches. Address this by starting with audit-only policies that monitor compliance without blocking actions. Build transparency and trust by participating in capability development from simple to complex, providing valuable insights and opportunities for all personas to contribute.
Skill gaps occur when staff need training in policy languages and associated tools. Invest in resources and workshops to build team expertise. Document extensively, providing clear explanations for each policy's purpose and implementation.
Implementation complexity overwhelms teams attempting too much too quickly. Start small with 5-7 critical policies addressing high-impact areas. Test rules thoroughly before rollout. Consider staged implementation where each phase has time for adjustment based on real-world feedback.
Inadequate executive sponsorship limits governance effectiveness. Establish clear C-level mandate from CIO, CTO, or CISO. Ensure governance team has authority to enforce policies and escalation paths for resolution.
Siloed operations prevent cross-functional collaboration. Build dedicated FinOps teams bringing together cloud architecture, security, operations, finance, and compliance expertise. Map governance efforts to FinOps efficiencies that demonstrate business value with less effort.
The rise of AI workloads in 2026 introduces new governance challenges. Organizations now face what industry analysts call responsible AI FinOps—managing AI cost and governance risk as a single, measurable system rather than competing concerns owned by different departments. This requires cross-functional teams jointly responsible for the entire lifecycle of high-risk AI products.
Building FinOps Culture Through Governance
Technology and tools alone do not create sustainable governance. Governance is fundamentally about culture—establishing attitudes and behaviors oriented toward driving business value from technology.
Transitioning from data center culture to FinOps culture requires policy and governance as the primary mechanism. Organizations with recognizable cultures demonstrate effective policy and governance frameworks. Without these frameworks, organizations cannot sustainably deliver business value from cloud.
Governance fosters collaboration between finance, engineering, and business teams while embedding shared accountability into daily operations. Everyone takes ownership for their technology usage. Teams collaborate around consumption, optimization, and value rather than working in isolation.
The FinOps governance framework works to align activities within cloud and intersecting scopes to overall business goals and strategies. It controls deployment and usage of resources to maximize ROI while ensuring predictable, manageable costs.
Success requires balancing quick wins with long-term cultural change through policy-driven behavior modification. Governance is a journey, not a destination. Organizations continuously reexamine maturity assessments for each capability, finding opportunities to reduce operational burden where possible.
How Opsolute Enables Comprehensive Governance
Opsolute provides comprehensive governance capabilities that turn FinOps theory into operational practice through integrated budget controls, intelligent cost attribution, and policy enforcement.
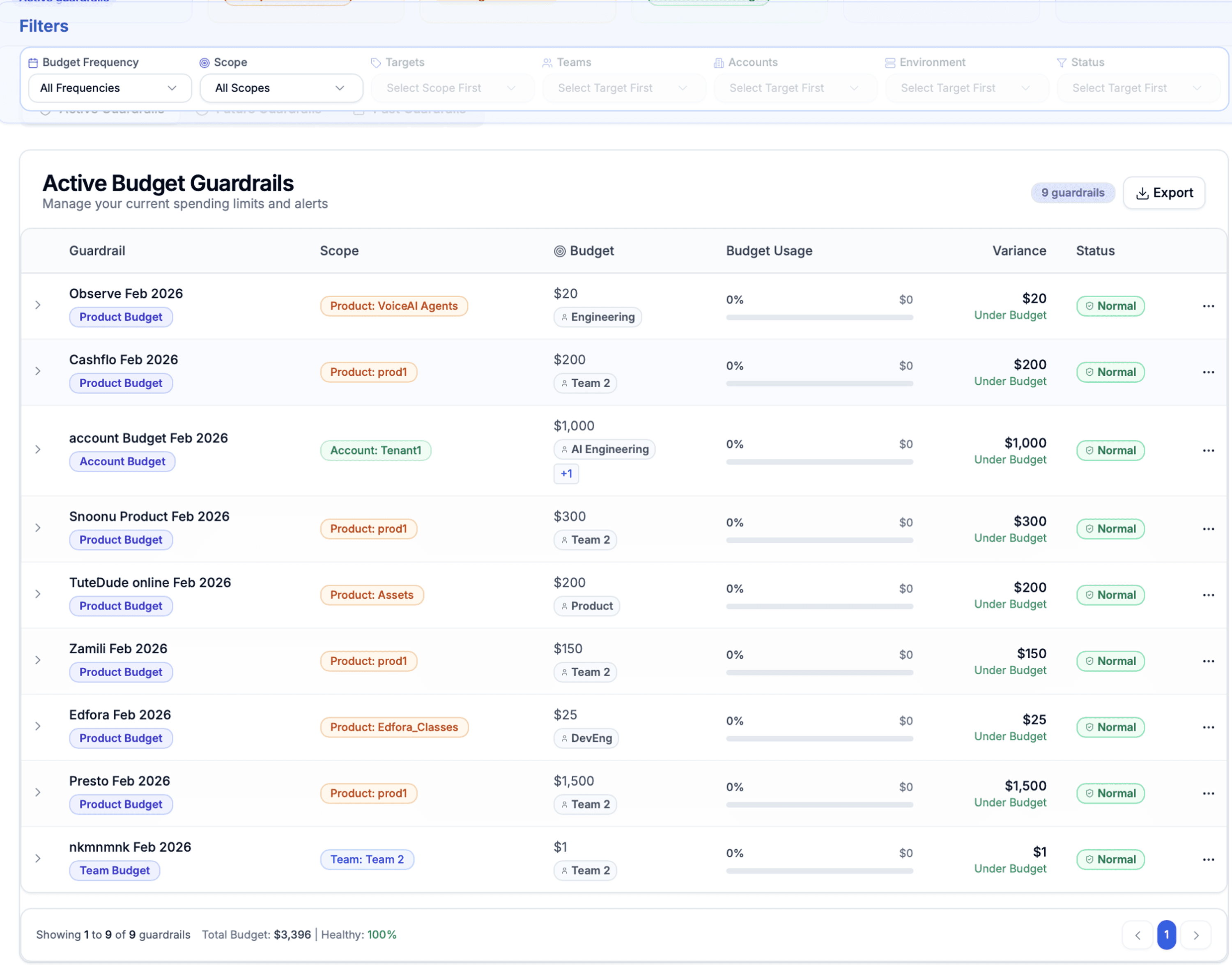
Budget Guardrails deliver multi-dimensional spending controls with real-time enforcement across accounts, environments, and teams. Configure threshold alerts at custom percentages to provide proactive warnings before budget breaches occur. Track active budgets, burn rates, and upcoming breach predictions through unified dashboards. Define granular budgets by scope with visual progress indicators, status monitoring, and variance calculation.
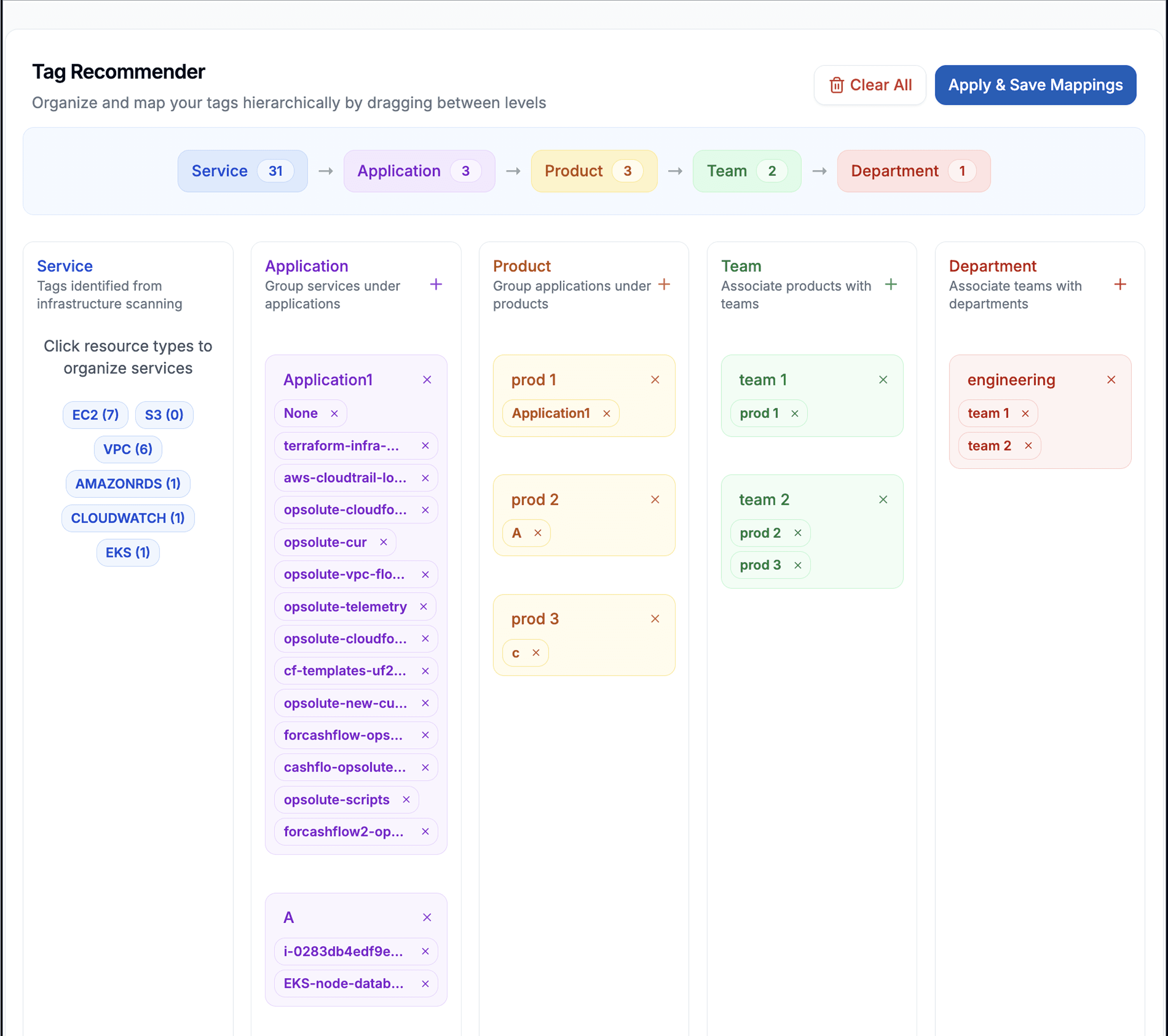
Policy and Governance features support tag management with Tag Recommender for ease of resource tagging and Tag Organizer to manage semantics across hierarchical layers. Tag-based resource management operates across application, product, team, and department dimensions. Track tag coverage and cost attribution per resource to ensure governance compliance.
Intelligent Showback enables hierarchical cost attribution with complete audit trails tracking reallocations. Multi-level cost breakdowns support budget allocation tracking and savings realization across entities. Claimed versus unclaimed savings attribution provides credit allocation to teams with category tracking for downsizing, reserved instances, spot migration, termination, and storage optimization.
These capabilities integrate with broader FinOps workflows including anomaly detection for real-time spending pattern analysis, forecasting for predictive analytics and budget reconciliation, and chargeback for cost allocation across teams, projects, and departments. The platform creates a cohesive governance ecosystem that scales with organizational maturity from Crawl through Walk to Run stages.
Frequently Asked Questions
Q: What is the difference between FinOps policy and FinOps governance?
A FinOps policy is a clear statement of intent describing how cloud-related activities should be executed to deliver business value. Governance comprises the processes, tools, and guardrails that enforce the policy and ensure desired behaviors occur. Together, they orchestrate and direct cloud financial activities.
Q: How do I start implementing FinOps governance without disrupting engineering workflows?
Begin with audit-only policies that monitor compliance without blocking actions. Start small with 5-7 critical tags or basic budget alerts, gather feedback, and expand gradually. Test rules thoroughly before rollout and use staged implementation where each phase has time for adjustment based on real-world feedback.
Q: What are the three enforcement mechanisms in FinOps governance?
Guidelines provide advisory best practices for policy implementation. Guardrails establish mandatory pathways for policy-compliant actions with potential consequences for non-compliance. Automation processes automatically enforce policies, removing manual burden and ensuring consistent compliance at scale.
Q: Which KPIs should I track to measure governance effectiveness?
Focus on a few strong indicators like percentage of compute costs covered by commitments (target 80%), percentage of teams trained on FinOps policies, tagging coverage rates, budget adherence percentages, and mean time to detect and resolve compliance issues. Avoid tracking too many metrics, which creates noise and inaction.
Q: How does the 2025 FinOps Framework update change governance requirements?
The 2025 update expands governance beyond traditional public cloud to Cloud+ environments including SaaS subscriptions, data centers, private clouds, and generative AI technologies. Organizations must now apply governance frameworks across multiple technology scopes while maintaining consistent financial accountability.
Q: What is the relationship between governance maturity and FinOps success?
Organizations with governance policies implemented across all FinOps personas operate at Run maturity with automated compliance, cross-functional alignment, and embedded best practices. Those without structured governance remain at Crawl or Walk stages with manual processes, reactive approaches, and limited scalability.
Q: How can automation help scale FinOps governance?
Automation through policy-as-code embeds governance into infrastructure provisioning, CI/CD pipelines, and daily workflows. Examples include auto-tagging resources, automatically shutting down non-production environments, preventing untagged resource deployment, and enforcing budget constraints before resources are created. This shifts governance left, preventing costly mistakes proactively.