The
Challenge
of
Cloud
Security
Economics
Digital defense costs often outpace security budgets as threats evolve.

Massive data transfer and storage costs from capturing every packet and log for compliance despite cloud cost optimization strategies.

Scaling for attacks often leaves "zombie" resources active long after threats are neutralized.

Overlapping AWS monitoring tools across clouds lead to duplicate resource consumption and fragmented spend.
Cybersecurity Value Propositions


RESILIENT & SECURE OPTIMIZATION
Infrastructure Risk Assessment
Analyzes dependencies to ensure rightsizing never impacts firewall or SIEM performance
LLM-Validated Recommendations
AI-verified optimizations aligned with NIST and SOC2 compliance standards.
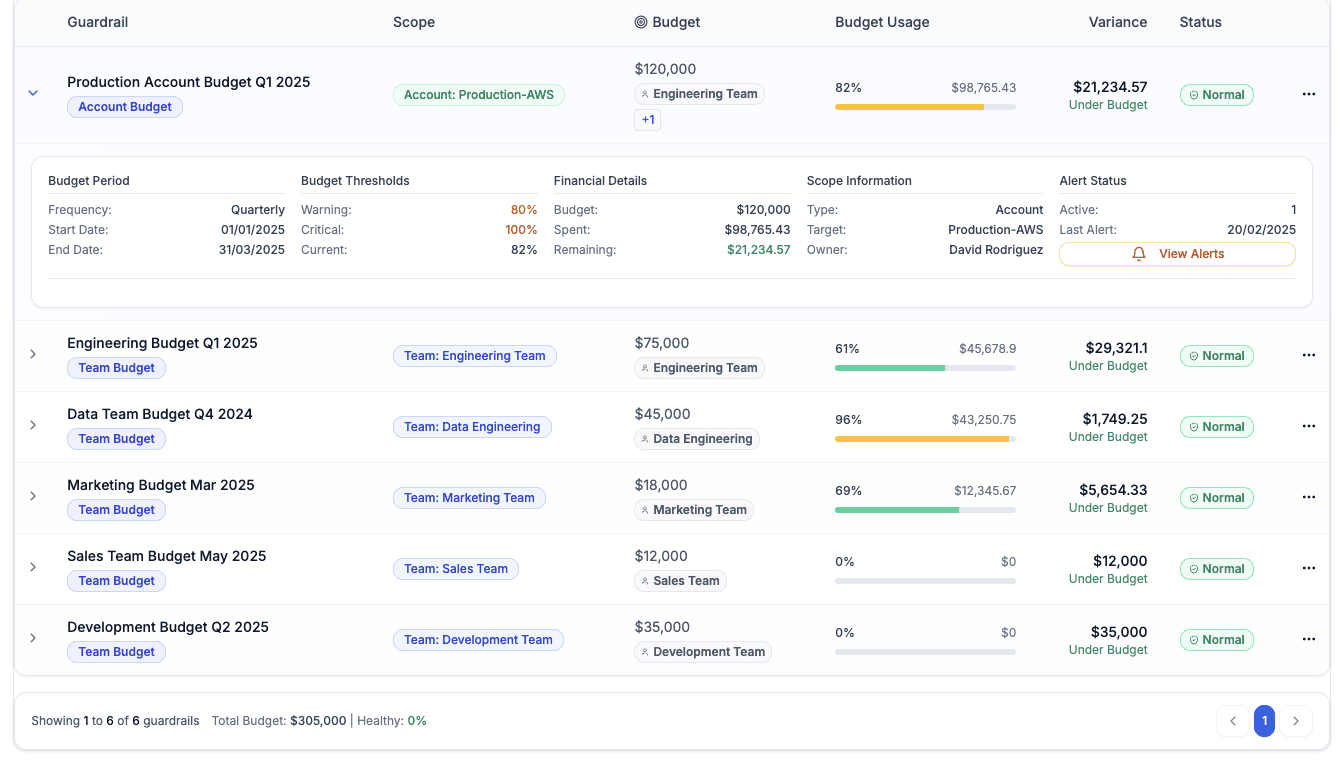
Safe Automation Guardrails
Protects security workloads with automated pre-deployment checks and stability testing.
Optimization Governance
Continuous cloud monitoring with rollbacks if threat-detection latency increases.
PRECISE ATTRIBUTION FOR SOC & MSSPS
Resource Relationship Mapping
100% visibility into resources supporting specific security products.
Tagging Intelligence
Automates resource clustering for specific security pods or regions.
Fair Cost Distribution
Accurate allocation of shared services like centralized logging or VPC peering.
Granular Budget Control
Enforce project-level limits to protect margins for security service providers.


THREAT-AWARE COST GOVERNANCE
Proactive Anomaly Detection
Real-time alerts distinguishing attack spikes from runaway cloud jobs.
Budget-Aware Forecasting
Predicts future spend based on historical threat and attack cycles.
Pre-Deployment Intelligence
See cost impacts of new security features or agents before production using cloud cost optimization tools.
Intelligent Waste Detection
Reclaims savings from idle sandboxes and overprovisioned lab environments using cloud cost optimization metrics.
Unifying
Security

Teams
with
Measurable
Outcomes
Budget Variance:
Achieve <5% variance between security budgets and actual monthly spend.
Forecast Accuracy
Monitor budgets, variance, and overruns without relying on spreadsheets.
Cloud Waste Reclaimed
Recover 30%–40% of spend from idle monitoring nodes and storage.
Commitment Utilization
Maintain >90% utilization for always-on security gateways and logging.
Learn

practical
approaches
to
cloud cost management
Practical guidance, real-world lessons, and FinOps thinking from teams managing cloud spend every day.




